The Exploit articles categorized as How To
-

Jailbreak Journey: Transforming an iPad for Mobile App Penetration Testing
By Jason Taylor Lead Penetration Tester Jason Taylor takes us step-by-step through jailbreaking an iPad 7 for use in penetration testing. June 3, 2025 -
PSE & Red Team Series: Physical Entry Bypass
By Nathan Anderson Raxis lead penetration tester, Nathan Anderson, continues our PSE & Red Team series with a discussion on the tools and techniques to bypass entry controls. April 8, 2025 -
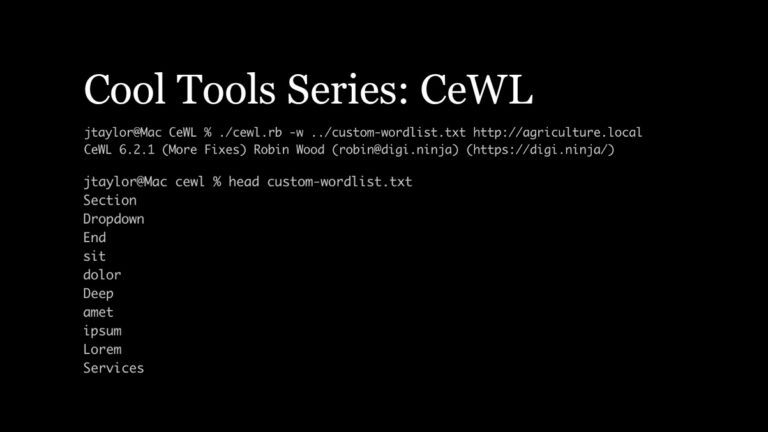
Cool Tools Series: CeWL for Penetration Testing
By Jason Taylor Lead Penetration Tester Jason Taylor discusses how the CeWL Custom Word List generator can improve hashcat results for penetration testing. March 25, 2025 -
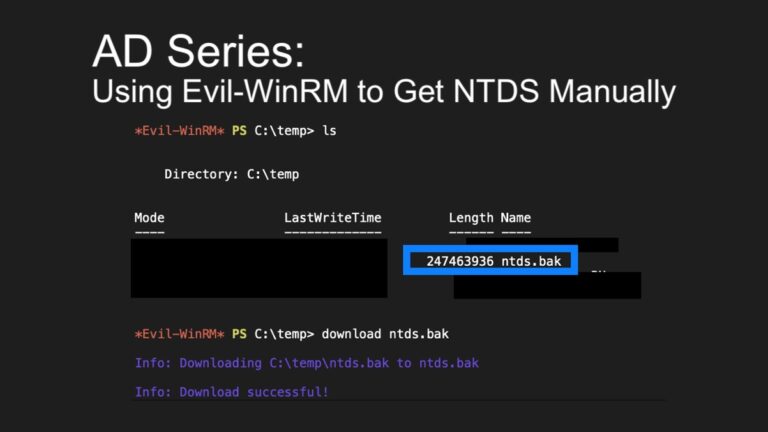
AD Series: Using Evil-WinRM to Get NTDS Manually in Penetration Tests
By Andrew Trexler Principal Penetration Tester Andrew Trexler’s Active Directory series is back, showing how to use Evil-WinRM to copy NTDS.dit manually in penetration tests. March 11, 2025 -
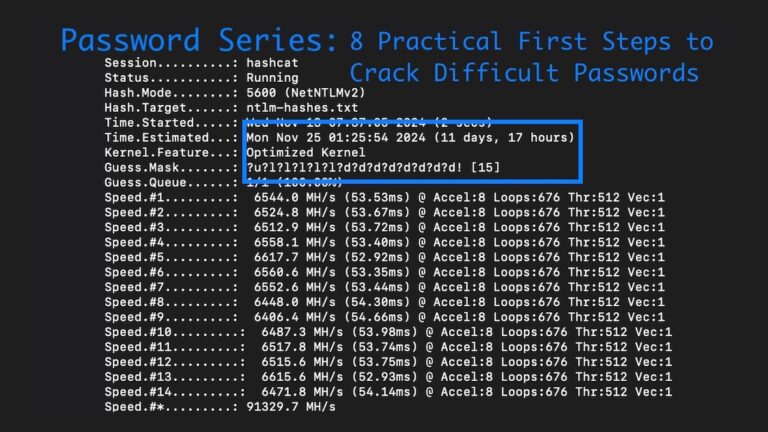
Password Series: 8 Practical First Steps to Crack Difficult Passwords in Penetration Tests
By Ryan Chaplin From rulesets & hardware to wordlists and mask attacks, Lead Penetration Tester Ryan Chaplin shows how to crack difficult password hashes in penetration tests. February 25, 2025 -

PSE & Red Team Series: OSINT & Reconnaissance
By Nathan Anderson Raxis lead penetration tester, Nathan Anderson, begins our PSE & Red Team series discussing the importance of OSINT and reconnaissance to begin the assessment. February 11, 2025