The Exploit articles categorized as Exploits
-

Deepfakes: The Face on Your Screen Might Not Be Real
By Scottie Cole Phishing and other social engineering techniques have crossed a threshold with deepfake attacks. Scottie Cole discusses how to protect your organization. April 17, 2026 -

Two Critical Telnet Flaws in 2026 Allow Unauthenticated Root Access
By Ryan Chaplin Lead Penetration Ryan Chaplin explains how to protect your network against CVE-2026-24061 and CVE-2026-32746, two critical Telnet flaws released this year. April 10, 2026 -

Five Things to Always Do After Getting Domain Admin
By Andrew Trexler So you got DA on your red team or internal network penetration test. Here are the five things that Principal Penetration Tester Andrew Trexler does next. March 24, 2026 -

BYOVD Attacks and EDR Evasion: Why Your Endpoint Security May Not Be Enough
By Brian Tant With Reynolds Ransomware in the wild, Brian Tant dives into BYOVD attacks, how they evade enterprise defense like EDRs, and what your organization can do. March 18, 2026 -

The Hidden Risks in Your Password: What You Type Matters More Than You Think
By Brad Herring Raxis has discovered and cracked our fair share of password hashes. Some that we have discovered may surprise you… and their bosses. Learn what not to do. March 10, 2026 -
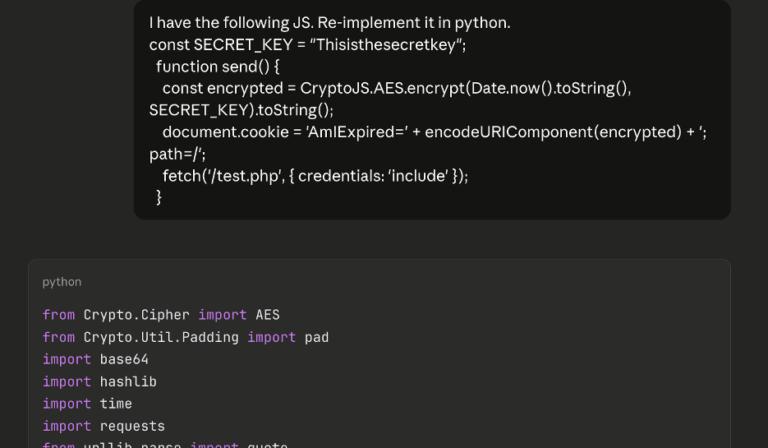
AI-Augmented Series: AI Scripting for Brute-Forcing on a Web App Pentest
By Andrew Trexler On a recent web app pentest, Andrew Trexler used AI to find client-side code that stopped his brute-force attack then used AI again to thwart that code. March 4, 2026