The Exploit articles categorized as Penetration Testing
-

Specialized Services: The Answer to Your Custom Cybersecurity Needs
By Caroline Kelly We love to hear that our cybersecurity services have been useful to our customers. See how a specialized device test was just that and how we can help you too. August 21, 2025 -
Raspberry Pi Planted in Failed ATM Heist
By Brian Tant Raxis CTO Brian Tant discusses the Raspberry Pi used in a recent ATM heist and how Raxis uses the same type of device in our pentesting. August 14, 2025 -

Choosing a Penetration Testing Company: Part 3
By Caroline Kelly Caroline Kelly concludes our three-part “Choosing a Penetration Testing Company” series with how Penetration Testing as a Service (PTaaS) provides great value. July 29, 2025 -
OWASP Top 10 for LLM Applications Penetration Testing
By Jason Taylor Lead Penetration Tester Jason Taylor looks at OWASP’s Top 10 list for LLM applications for penetration testing as AI machine learning becomes prevalent. July 15, 2025 -

Choosing a Penetration Testing Company: Part 2
By Brad Herring Brad Herring continues our three-part “Choosing a Penetration Testing Company” series with a look at the factors to consider when choosing the best vendor. July 1, 2025 -
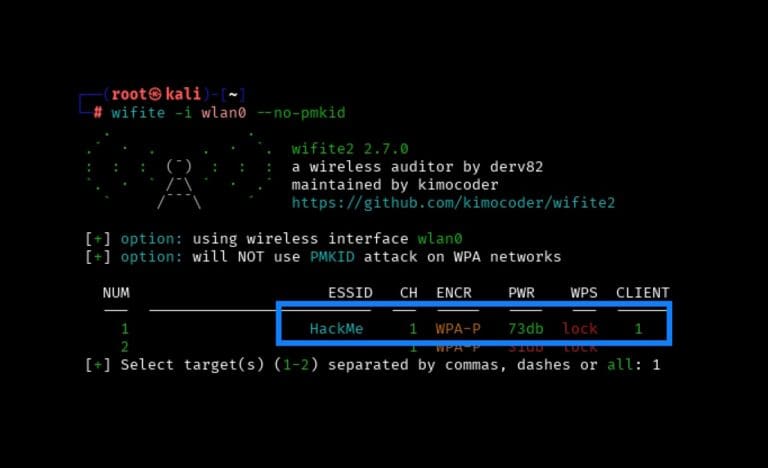
Wireless Series: Using Wifite to Capture and Crack a WPA2 Pre-Shared Key for Penetration Testing
By Scottie Cole Principal Penetration Tester Scottie Cole begins our wireless penetration testing series with capturing and cracking a WPA2 Pre-Shared Key using Wifite. June 17, 2025